Hacker of US Supreme Court System Sentenced to Probation After Bragging on Instagram
Key Takeaways
- Nicholas Moore hacked multiple U.S. government networks, including the Supreme Court's filing system, using stolen credentials.
- He publicly boasted about his cybercrime on Instagram, sharing victims' personal data.
- Moore received a sentence of probation, sparking discussion about penalties for high-profile cyber intrusions.
- The case highlights ongoing vulnerabilities in federal cybersecurity infrastructure and the threat of personal data exposure.
- The incident underscores the critical need for robust cybersecurity defenses across government institutions.
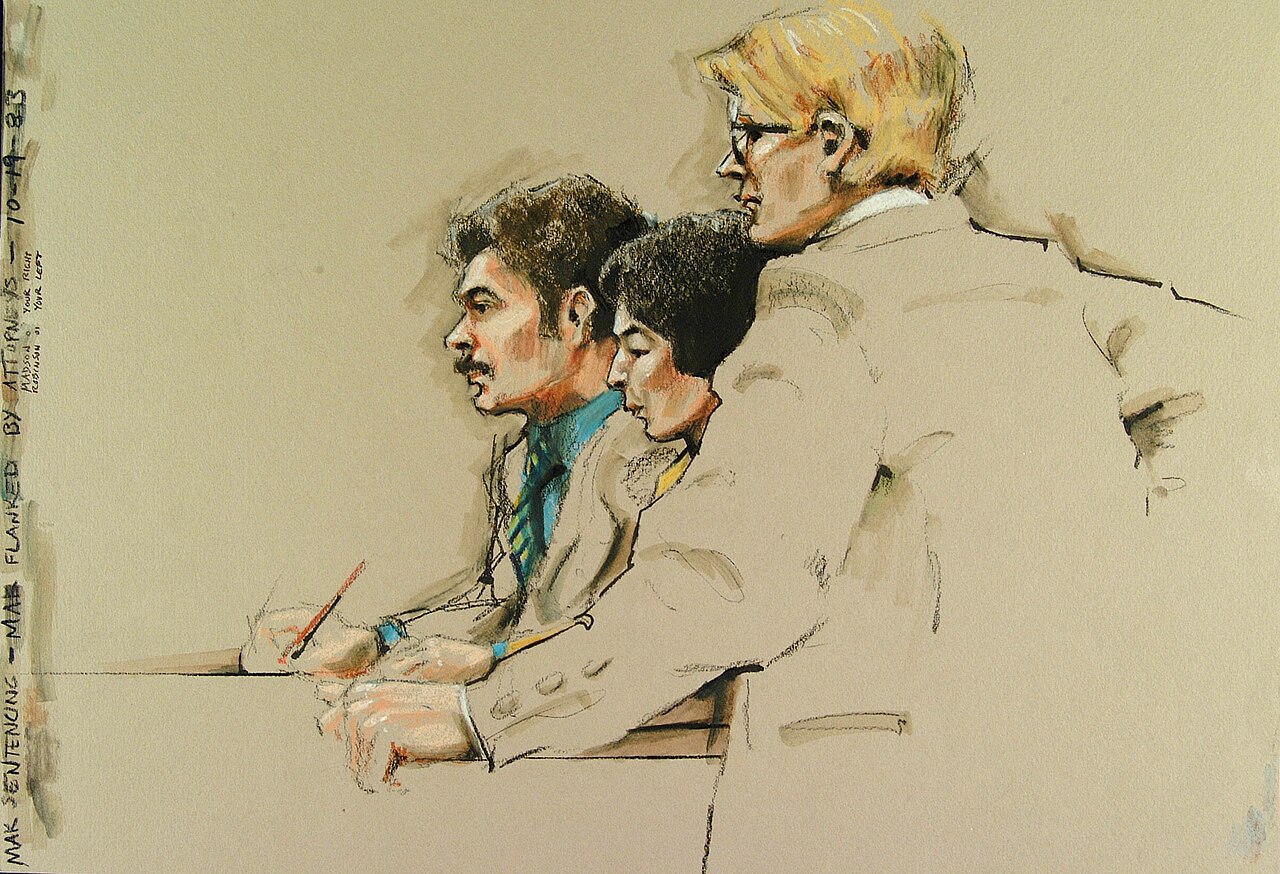
WASHINGTON D.C. – Nicholas Moore, the individual who breached at least three U.S. government networks, including a filing system for the U.S. Supreme Court, has been sentenced to probation. The sentencing concludes a case that underscored persistent vulnerabilities within federal cybersecurity infrastructure and raised questions about the appropriate penalties for such high-profile digital intrusions.
Moore gained unauthorized access to the governmental systems by exploiting stolen credentials, a common but often effective method employed by cybercriminals. According to court documents and statements, his activities extended beyond mere penetration. He notably boasted about his exploits on social media, specifically Instagram, under the handle @ihackedthegovernment, where he allegedly posted personal data belonging to his victims. This public display of his illicit activities not only drew attention to the breaches but also exacerbated the harm to those whose information was compromised.
The breach of the Supreme Court's filing system is particularly alarming, as it involves an institution at the pinnacle of the American judicial system. While the full extent of the data compromised and its potential impact on national security or legal processes has not been entirely disclosed, such an intrusion raises serious concerns about the integrity and confidentiality of sensitive government information. The incident highlights the ongoing challenge faced by federal agencies in safeguarding their digital perimeters against sophisticated and sometimes brazen cyberattacks.
The decision to impose a sentence of probation, rather than incarceration, on Moore has drawn attention. Typically, probation involves a period of supervised release, during which the convicted individual must adhere to strict conditions, which often include refraining from computer use without permission, performing community service, and undergoing counseling. Legal experts suggest that such a sentence could be influenced by various factors, including the defendant's cooperation with authorities, lack of prior criminal record, the specific nature of the data accessed, or efforts made toward restitution.
This case serves as a stark reminder of the continuous threat posed by cyberattacks, whether from state-sponsored actors, organized crime syndicates, or individual hackers. It compels government entities to continually reassess and fortify their cybersecurity defenses, investing in advanced protective measures and employee training to prevent similar breaches in the future. The public dissemination of stolen personal data, as seen in Moore's case, further emphasizes the critical need for robust data protection protocols to shield citizens from privacy violations and potential identity theft.
Law enforcement agencies continue to prioritize the prosecution of cybercriminals, aiming to deter future illicit activities. However, the outcome of cases like Moore's often sparks broader discussions within the cybersecurity community and legal circles regarding the effectiveness of current judicial frameworks in addressing the evolving landscape of digital crime. The incident underscores that even the most secure institutions remain targets, necessitating constant vigilance and adaptation in the face of persistent cyber threats.
TRENDING POSTS

SoftBank's €75 Billion Bet on French Data Centers
SoftBank plans a massive €75 billion investment into SoftBank France data centers, aiming for 5 GW capacity. Discover the strategic implications and what this means for Europe's digital future.

Keychron K2 HE Concrete Edition: Is Concrete the New Gold?
Discover the Keychron K2 HE Concrete Edition, an innovative keyboard redefining design. Learn how this unexpected material impacts typing feel and the future of peripherals.

5 Moves Disney Must Make After The Mandalorian Success
Discover what's next for The Mandalorian and Grogu

Blue Origin New Glenn Explosion: What It Means for Space Race
A recent Blue Origin New Glenn explosion during testing marks a significant setback for Jeff Bezos's space venture. Discover the full implications.

Privacy-Conscious Gay Dating Apps Challenge Grindr's Reign
New privacy-conscious gay dating apps are rising to challenge established giants, prioritizing user data and community. Discover why users are shifting.

Top Memorial Day Tech Deals Revealed: What You Missed
Uncover the most significant Memorial Day tech deals on everything from OLED TVs to smart home devices. Don't miss out on these limited-time savings!